Penetration test raw data
Protect your data by hiring the right penetration test vendor
2 Oct Never make up or falsify data in a penetration test. Never reuse In these situations, the raw tool output will provide the bulk of your report.
Recommended Posts


Without appropriate penetration testing, though, they have . finding. Re-test. We can provide access to our testers and the raw test data to support and expedite.


Hi guys Shirley Age: 28. I am just a normal girl whit t-shirt and jeans hehe.I would like to inform you that i am not interested of quantity of offers.Beautiful face with perfect soft skin to match!My name is Alexis


Eliza Age: 18. who is charming, smart and successful, then drop me a line with your idea about our first date :)My name is Crystal

Penetration testing - raw data storage structure - Business and Enterprise IT - Hak5 Forums
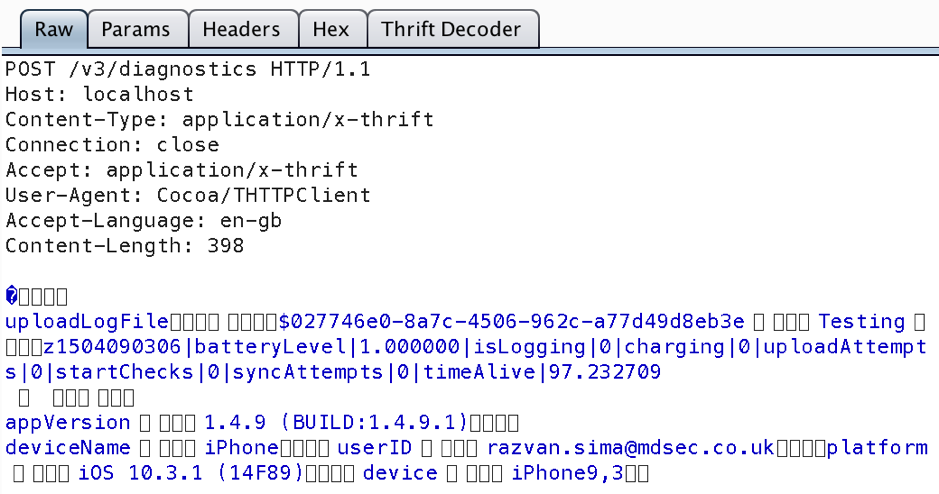


15 Mar Why would someone that doesn't administer the network want to be the only person that gets to see the raw data of the pen test results?.
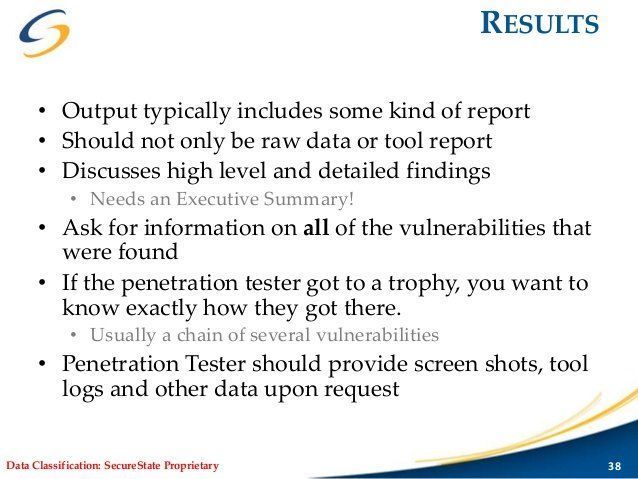
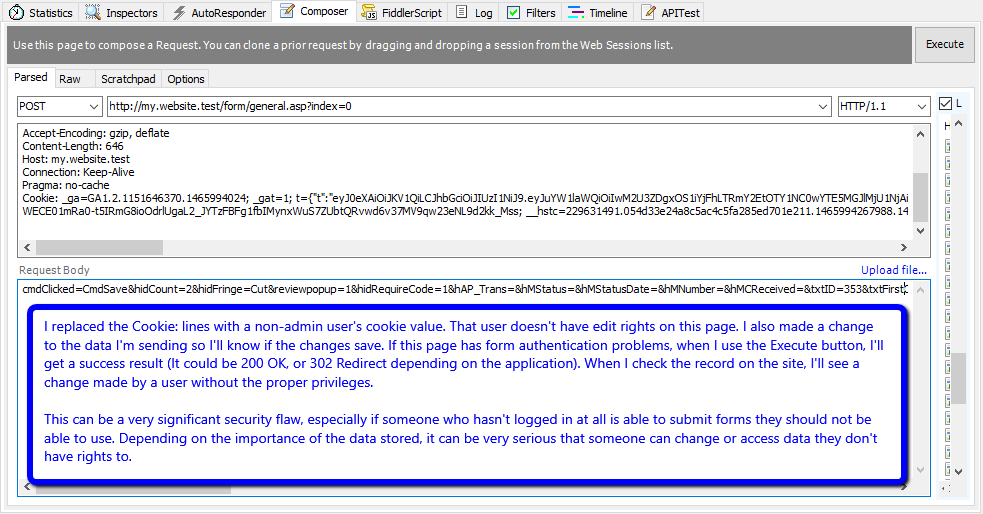
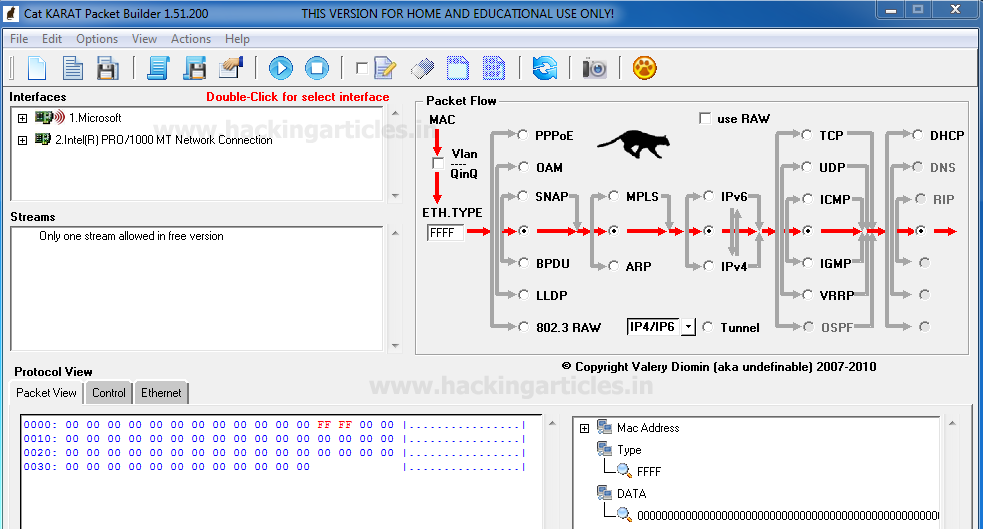
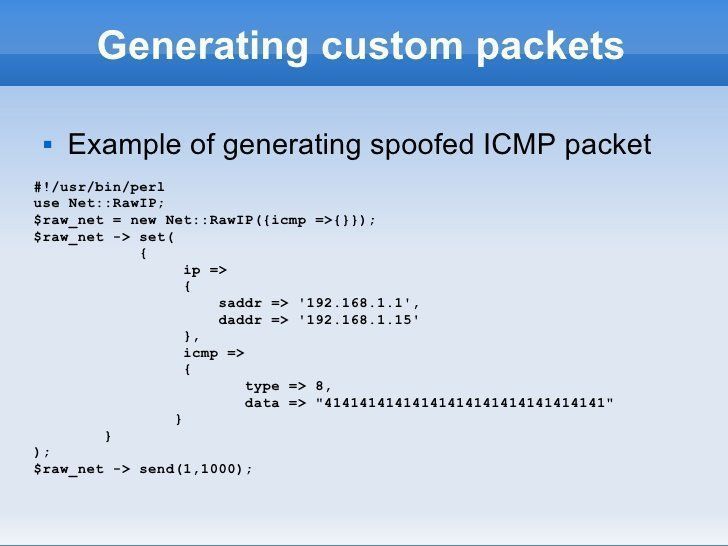
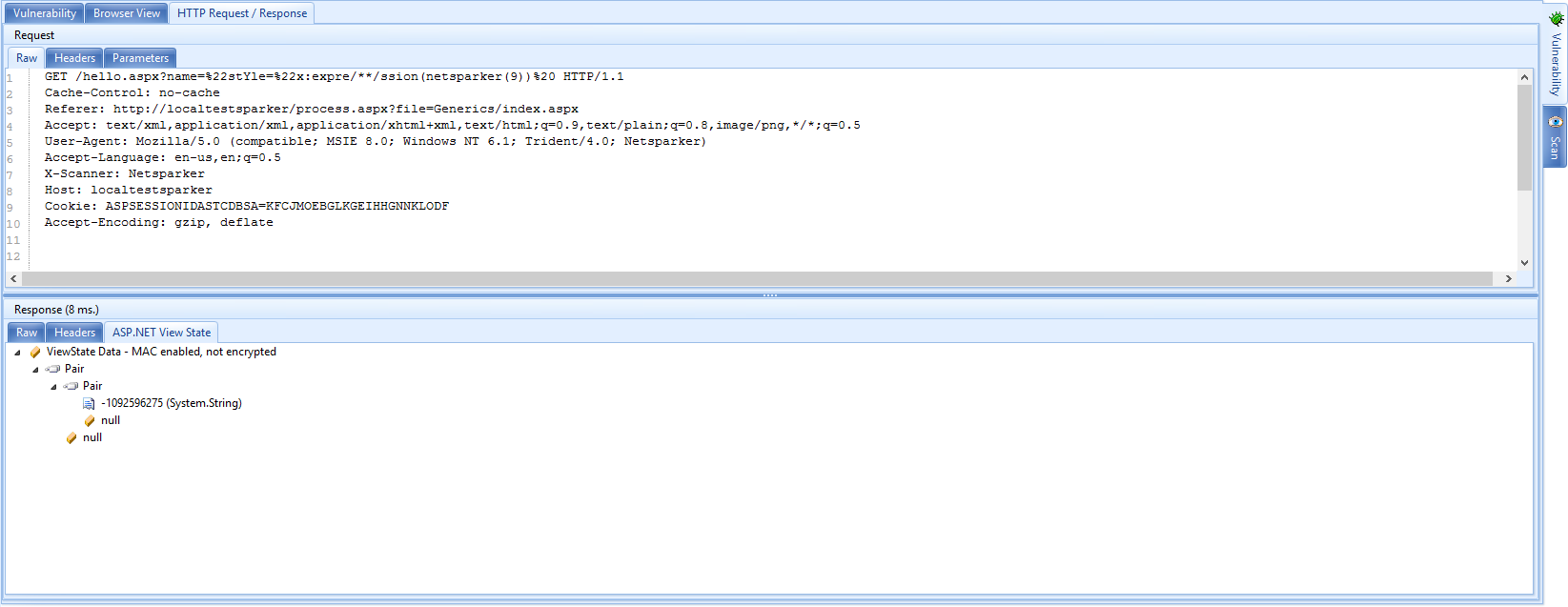
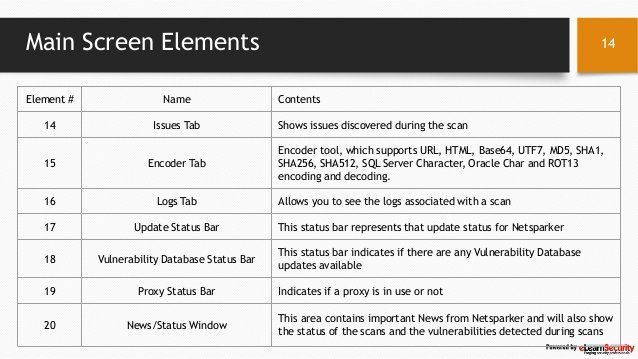
Description:Many penetration testers mistakenly think that they can simply provide the raw output from the tools that they run. This group of people will often collect and neatly organize the various outputs into a single report. They will gather any pertinent information from the reconnaissance phase and include it along with the output from nmap and Nessus. Many of the tools we discussed in this Post include a reporting engine. For example, Nessus has several prebuilt reports that can be generated based off of the scan. Unfortunately, using the prebuilt reports is not enough.





























User Comments 3
Post a comment
Comment: