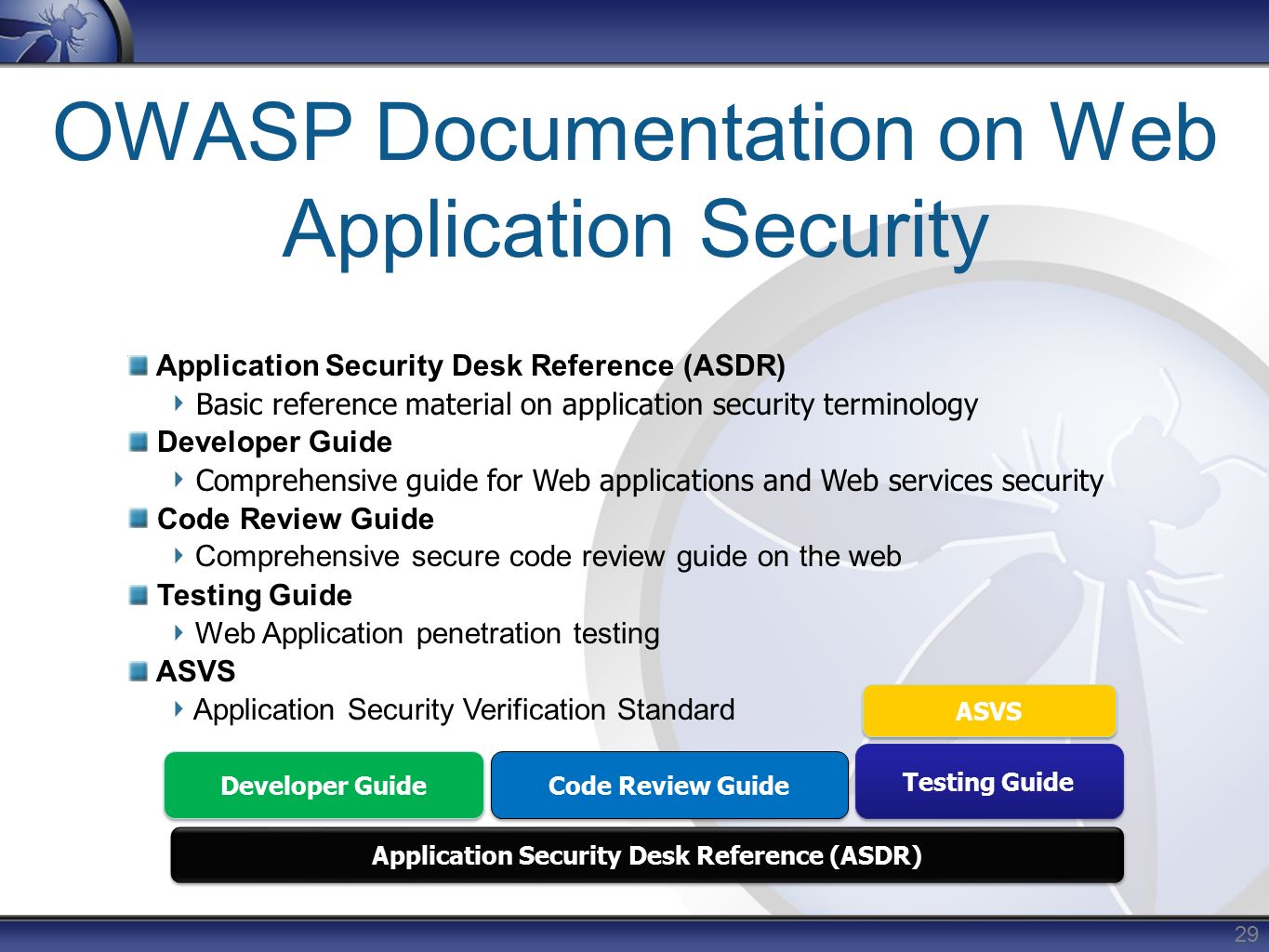
Application developer guide penetration security tester web
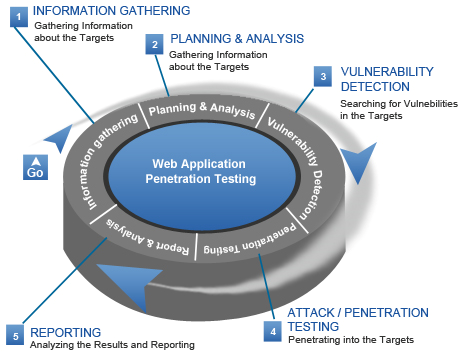
5 Aug This article is part of the new OWASP Testing Guide v4. the 12 subcategories of the Web Application Penetration Testing Methodology.



Willa Age: 24. The quality is absolutely essential for me as well as for you.My name is carolina aurora, independent companion based in prague who is available for incall and outcall meetings in prague only and iam very glad that you came into my europedates profile.I like men who have a good sense of humor, love adventure and know how to please a woman.Incall, outcall, sex in different positions,anal, blowjob, oral without a condom, oral with condom, oil massage, kiss, kissing with tongue, come on body, come in mouth, position, foot fetish, masturbation, golden shower, extraballs, footjob, ball Licking and Sucking, girl friend experience, light domination and many other interesting )))
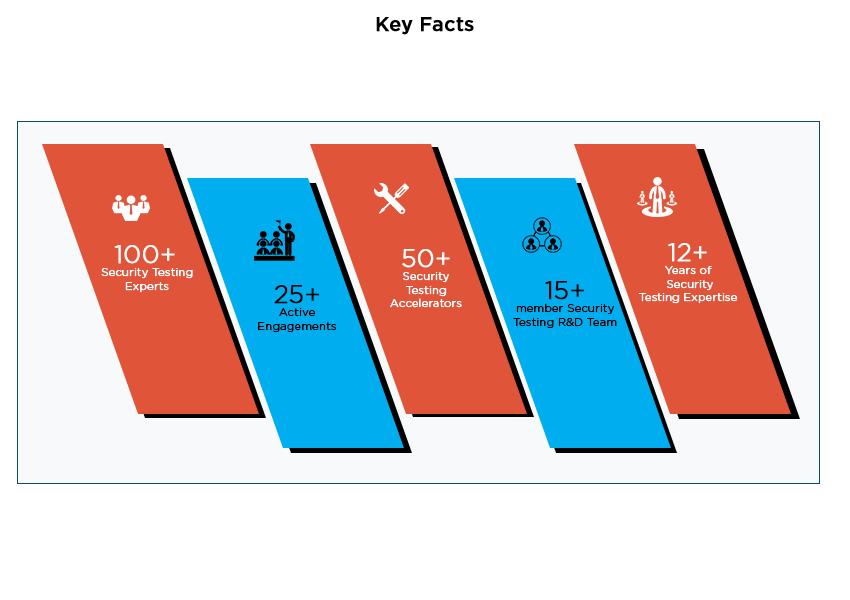
Application Security Testing Tools | Veracode

Donna Age: 28. I like candlelight dinner -where you can enjoy a challenging conversation, laugh and fun with an elegant, smart and erotic lady.My name is Kiki(If by phone: please note sms only.Hello, i'm an independent beautiful escort from Bucharest






Navigation menu
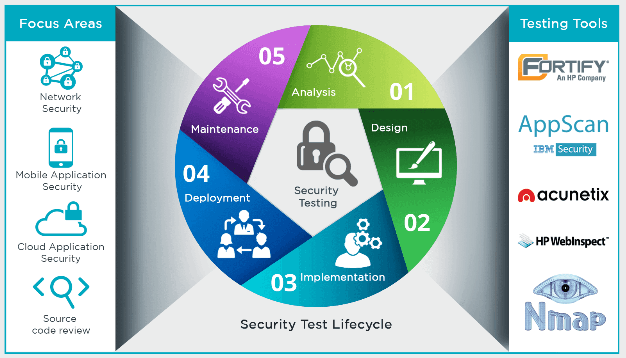
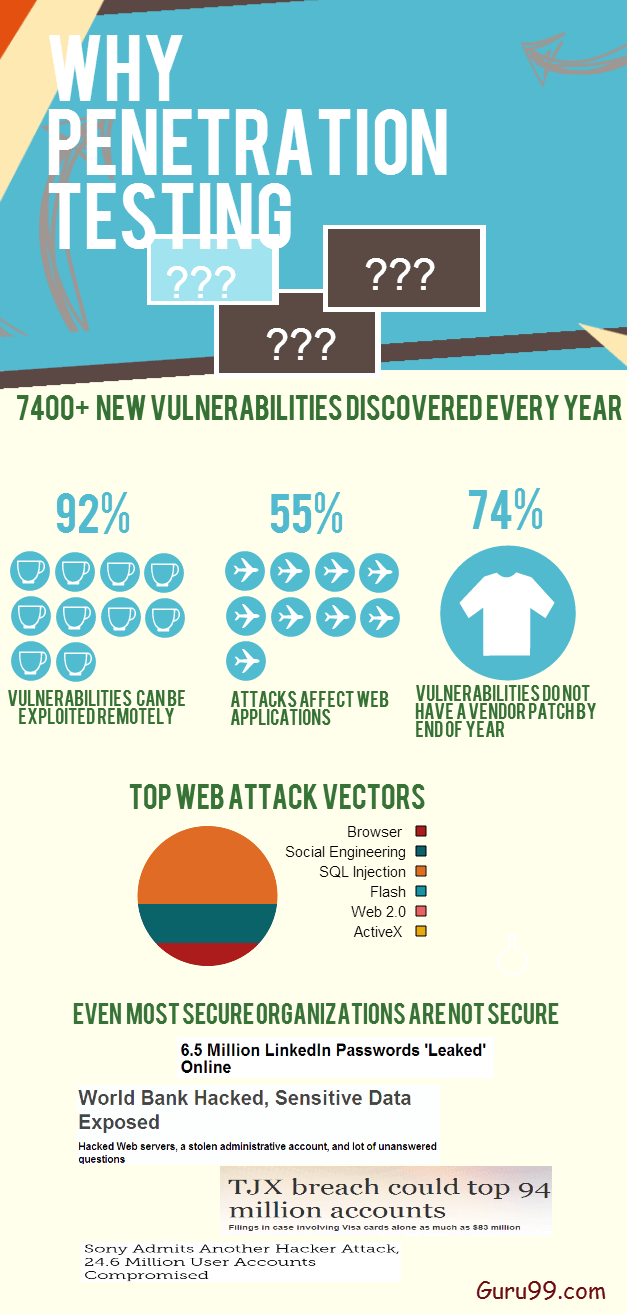
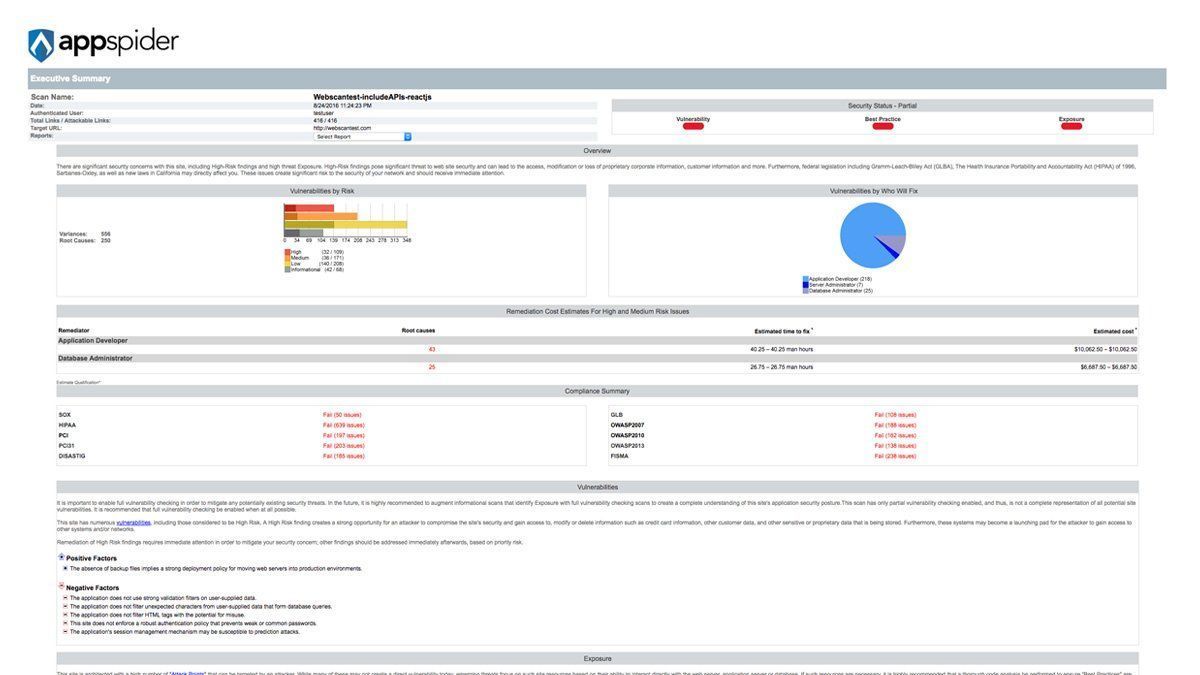
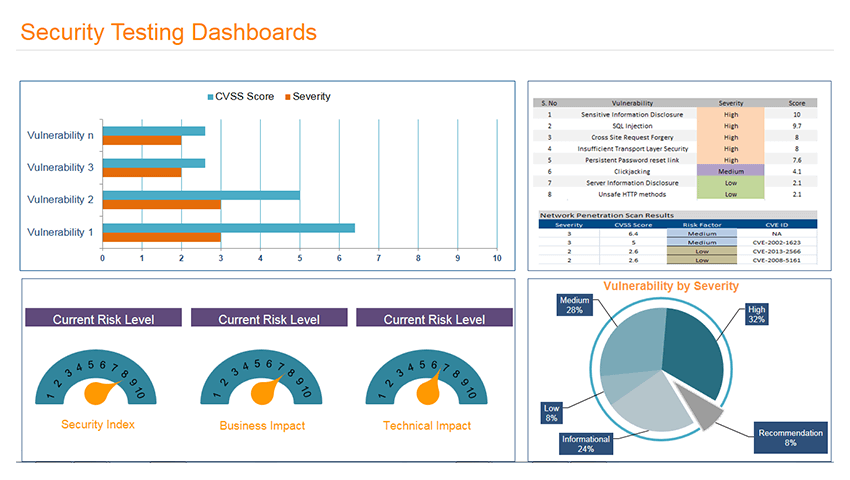
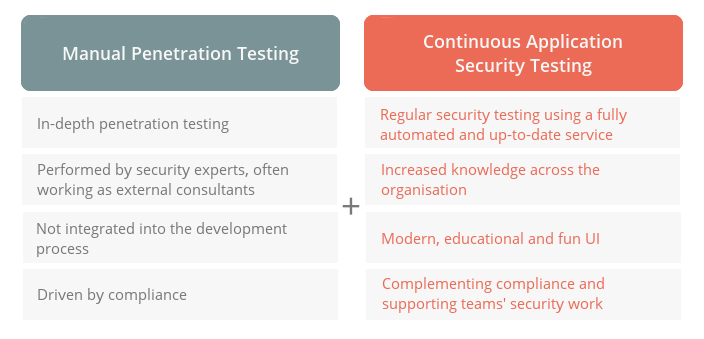
Description:A web application pen test, or penetration test, should be part of a rigorous software security testing strategy. While automated testing technology can find many flaws and vulnerabilities in web applications, it takes a web application pen test to find certain business logic flaws and problems with authorization issues that can lead to security breaches when left unfixed. Best practices for web application security suggest conducting a web application pen test at least once per year for each application. The challenge for application security teams is coming up with the resources for annual web penetration testing.


























User Comments 3
Post a comment
Comment: